this post was submitted on 16 Oct 2023
1760 points (99.3% liked)
internet funeral
6912 readers
1 users here now
ㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤㅤart of the internet
What is this place?
• !hmmm@lemmy.world with text and titles
• post obscure and surreal art with text
• nothing memetic, nothing boring
• unique textural art images
• Post only images or gifs (except for meta posts)
Guidlines
• no video posts are allowed
• No memes. Not even surreal ones. Post your memes on !surrealmemes@sh.itjust.works instead
• If your submission can be posted to !hmmm@lemmy.world (I.e. no text images), It should be posted there instead
This is a curated magazine. Post anything and everything. It will either stay up or be lost into the void.
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
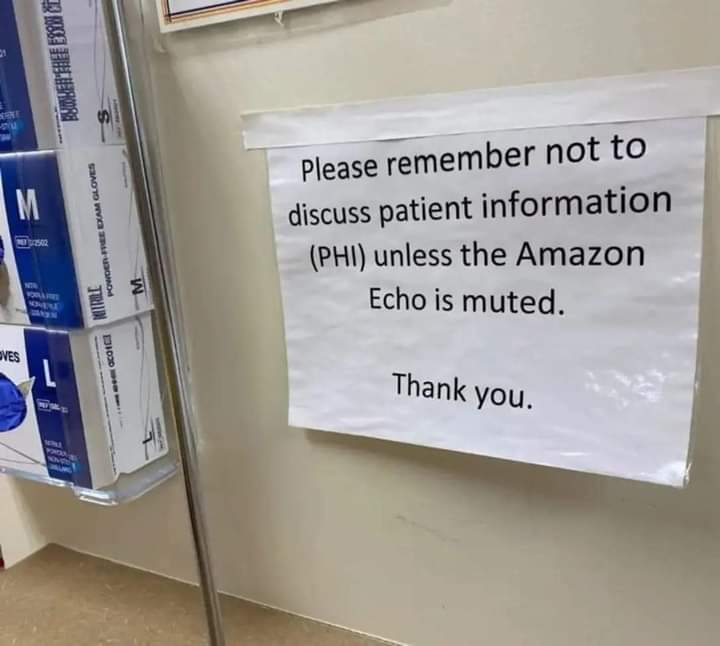
Curious to learn how would you verify it. Wouldn't one has to go as low level as power spikes? Not to sound paranoid but one can't just believe the PR these companies said. Consequently we have to check how the device behaves. It's not because it doesn't send information that it does not process it. One could imagine it logs on specific behavior or keywords and only send information back when "normal" behavior is expected, e.g update check. I'm not trying to imply this is the case, only that verifying doesn't seem "easy" to me.
You can check network activity while it's muted and while it's not muted to see when it's phoning home. And if you're still worried, keep it on mute for an extended period of time and then turn it on again to see whether it transmits the backlog or not. Easy to proof.
Are you saying the size of the upstream packet should be proportional to the mute time? Wouldn't that assume that one knows ahead what such logs include or not? For example if we imagine that the device is listening while on mute for the keyword "potato" and it's not being said once during the mute period, wouldn't that still making an upstream packet of a fixed length, i.e zero, despite being actively listening and able to phone home? Genuinely trying to understand how one can be so confident based solely on packet size as this seems to make some assumption on how the device behaves.
Edit: regardless, monitoring traffic (which I already mentioned, hence aware of but arguing it's not sufficient) using Wireshark or netcat is definitely not "easy" for most people buying such devices.
If the device monitors despite being on mute and does not send packets home while on mute, then it would send more when turned back on, yes. How else would the logged information reach the datacenter? Also, not everyone buying an Echo needs to do an analysis, it's enough if a random tech-savvy person does it. Unless you argue they purposefully build surveillance devices and mix them with devices that are what they claim to be to obfuscate this behavior.
The conspiracy theory is about the muted device spying on you, not whether the activation phrase is recognized while muted. Or maybe I am misinterpreting this comment chain.
I don't think so, here is another example, what if the device counts how many times someone said "fuck", then sending {fuck:0} or {fuck:4,294,967,295} will result in the same size of data being transmitted. In fact imagining that the device is designed to do so, it could always send a large meaningless packet on querying for updates just so that when it actually needs to send data, it would look similar, same approximate number and lengths of packets and can be capped. I'm not saying it's the case now, just technically feasible and I believe hard to detect.
Also on "trusting" someone then answered in https://lemmy.world/comment/4594899 but I'd said it's also not "easy". At least one must trust their institutions able to vet on the person able to review such devices and that the device tested and the one used are actually identical.
Finally I'm not arguing for conspiracy theory or that Echo is spying on users, only that verification for privacy on closed system is not "easy" either through trust of 3rd parties or technical expertise for an "average" user, not somebody working in the domain.
The sources people use here seem to confirm it being a hardware mute that cuts off power to the mic. https://iot.stackexchange.com/questions/2382/is-the-amazon-echo-mic-mute-a-hardware-switch
Well that's arguably "easy" but then one must trust these people and thus either know them and their motives or understand the underlying technology (and thus not needing their expertise) so I'd say no really "easy".
I mean, it technically is listening for the wake up words, like "Ok Google," but nothing is transmitted when in that mode. Only when the wake up word is uttered, then a network connection is established.
I read an article about an independent auditor making these tests and writing about the results.
Of course, and to be fair, the devices' behavior may have changed recently. But I haven't heard anything about it yet.
Having said that, since we're talking about the mute button, someone else already mentioned that the mute feature is hardware-based.
No, the microphone literally stops converting sound to electrical signals in that mode. The mute button causes a hardware disconnect; if the mute light is on, the microphone is literally unpowered.
Which is what I mentioned in my very last sentence, yes.
No software update could bypass such a hardware feature, which is exactly why it was designed thusly.
Huh? It was built that way, and it does it. It's a hardware feature.
Your reading comprehension is terrible.
I am not just talking about the pushbutton.
I am stating that the mic power is literally disconnected in mute mode. The indicator LED physically cannot light up unless the power is cut. This is all implemented directly in hardware. This has been torn down by hardware enthusiasts and verified for many, if not all, Echo devices. I've also personally reviewed the schematics of multiple Echo devices.
A hardware circuit like that cannot be modified by any software, because there is no software involved in it.